Crypto staking involves locking up PoS tokens to support a blockchain’s operations, such as validating transactions and producing blocks. Rewards correlate with stake size, lockup duration, and network parameters. Staking models range from direct validators to delegated arrangements, each with distinct risk and governance implications. While yield, volatility, and validator performance matter, understanding incentives, penalties, and security risks is essential. The topic remains nuanced, inviting further analysis of models, economics, and practical safeguards.
What Is Crypto Staking, in Plain English
Crypto staking is the process by which holders of a proof-of-stake (PoS) cryptocurrency commit their tokens to support network operations, such as validating transactions and producing new blocks, in exchange for rewards.
The approach distills staking basics into observable mechanics: locked assets, validator selection, and periodic rewards.
It emphasizes reward fundamentals, risk exposure, and measurable yield under varying network conditions.
How Staking Works and Why It Matters
How staking functions and why it matters can be summarized as a mechanism by which PoS networks allocate validation duties to token holders, thereby securing consensus and governance.
The process translates stake into influence over block production, rewards, and penalties, shaping staking economics and validator economics.
Network security relies on economic alignment, incentive compatibility, and transparent parameterization for resilient, scalable governance.
Staking Models: From Proof of Stake to Delegated Options
Staking models vary in how validation duties, rewards, and governance influence are distributed among participants. Proof of Stake assigns block validation to stake qualifiers, with delegators and validators forming shared incentives. Delegated Options shift oversight to chosen representatives, altering stake penalties and incentives. Performance metrics, validators performance, and slashing across architectures shape security, throughput, and participant trust in decentralized networks.
Risks, Rewards, and Safety Tips for Beginners
Risks, rewards, and safety considerations for newcomers to staking are quantifiable and multifaceted: potential yield depends on network parameters, asset volatility, and validator performance, while exposure includes slashing, lockup periods, and opportunity costs.
The landscape reveals uninformed fraud and centralized risks, demanding rigorous due diligence, diversified validators, and transparent governance; adherence to protocol metrics, governance participation, and risk budgeting enable measured, freedom-oriented participation without overexposure.
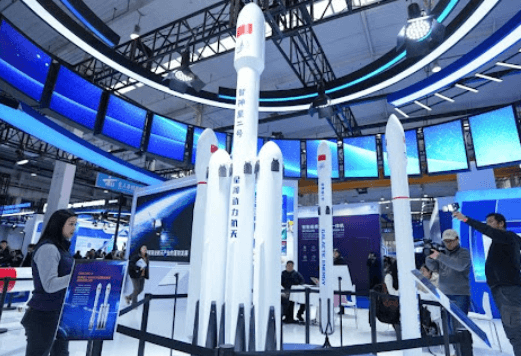
See also: The Rise of Commercial Space Technology
Frequently Asked Questions
How Do Staking Rewards Affect Tax Obligations Across Countries?
Staking rewards taxation varies by jurisdiction, with tax treatment differences shaping reporting; cross border compliance challenges arise. Custodial vs non custodial setups influence liquidity risk considerations, while staking rewards taxation and related policies dictate compliance and liquidity planning.
Which Coins Support Non-Custodial Staking Options?
Non-custodial staking options exist for several networks, including Ethereum 2.0, Solana, Tezos, and Cardano; users retain control of keys. Staking rewards impact tax reporting, with varying treatment by jurisdiction and reporting standards.
Can You Stake Through an Exchange or Must You Use a Wallet?
Yes, staking can be done through exchanges or wallets; both routes yield staking rewards, though liquidity, control, and security differ. Tax obligations apply regardless, with reporting dependent on jurisdiction and whether rewards are treated as income or capital.
What Are the Liquidity Implications of Locked Staking Periods?
Liquidity implications of locked staking periods: staking liquidity is constrained until maturity, affecting liquidity timing and fund accessibility; opportunity costs rise as capital remains staked, while market volatility may stress reward baselines and exit options for freedom-seeking investors.
How Do Slashing Events Work in Different Networks?
Slashing mechanisms vary by protocol, applying validator penalties for misbehavior or downtime; network penalties deter infractions, while governance rights may be weighted post-penalty. Data-driven assessments compare slashing thresholds, reward impacts, and validator risk across networks. Freedom-minded observers note transparency trade-offs.
Conclusion
In sum, crypto staking aligns economic incentives with network security, tying validator performance to rewards and penalties. Data shows higher staking returns correlate with perceived protocol robustness and lockup terms, while risks include slashing, liquidity constraints, and validator risk. From PoS to delegated models, staking shapes governance influence and monetary dynamics. As the adage goes, “don’t put all your eggs in one basket”—diversification and diligent validator assessment remain essential for risk-aware participation.